Ever came across a website only to be met with a message that says that the content is blocked in your region? Yup, that had me using VPNs in the first place but as much as time passes by I came to know that they also provide you with security and privacy on the internet so that you are safe from prying internet eyes.
Related: 11 Top Best Paid VPNs in 2026
As a freelance web developer and tech geek, I use VPNs as my daily tool to roam around the internet to communicate with my clients. I have been using them for a while now and it is a worthy investment that you could do but yesterday it occurred to me that aside from giving me privacy and security what even is VPN and how does it work? Should people trust someone to hide their IP address?
So in this article, I aim to explain the basics of VPNs so you can learn more about this technology and how it is useful for other reasons.
In this guide:
What Is VPN?
VPN also stands for virtual private network allows you to establish a secure network connection when using a public network. Connecting a VPN impersonates your online presence and encrypts your internet traffic.
By using VPN it is difficult for third parties to track your online activities or steal your data. What could be better than an encrypted server that hides your IP address from different co-operations, government agencies, and hackers? That is where VPN protects your data at every cost possible from prying internet eyes.
It doesn’t stop here VPNs can also be used to bypass geo-restrictions and censorship which let users access blocked or restricted content on the internet. In this era of technology where you have money in your bank accounts that can be accessed through the internet or your online presence which could let hackers or co operations know your location is a threat to your daily life that is why VPNs are essential tools that keep your identity on the internet low and let you have a safe environment on the internet with security and privacy. So before getting into how many types of VPNs are available, we should know how it works.
How does a VPN work?
Since we already know what is a VPN and how it helps us we should know how it works. A VPN hides your IP address by letting it go through a remote server run by a VPN host which lets you surf online with a VPN that makes a VPN server the source of your data.
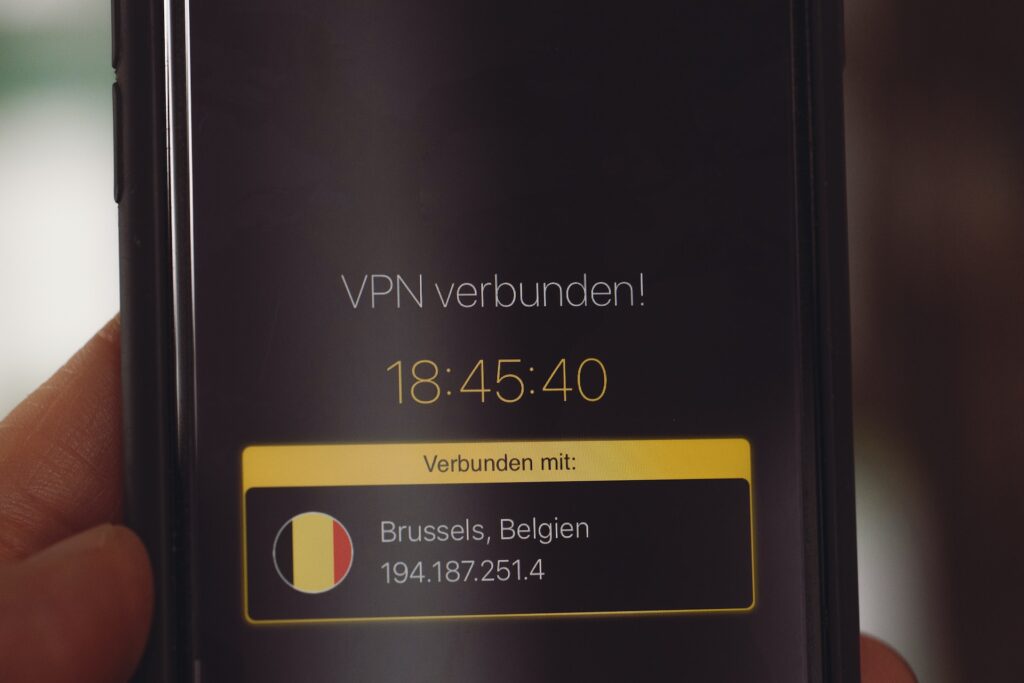
Even your internet service provider or anyone on the network can not access your data or which website you visited because it will convert into gibberish which will be useless to them.
However, it occurs to many people how can we trust the VPN to be the source of our data? All you have to do is to research your VPN provider and which protocols they use so before you search about them I have already explained every trusted type of protocol that could be used in our modern world.
Types of VPN:
If you’re a regular user and just want to use and enjoy the benefits of a VPN, you may not be interested in knowing the types of VPNs. But if you’re a nerd or maybe just interested in learning more about it, we’ve compiled some types of VPN that may help you learn more about it.
- Remote Access VPN
- Site-to-site VPN
- Internet Protocol Security (IPSec)
- Layer 2 Tunneling Protocol (L2TP)
- Point-to-Point Tunneling Protocol (PPTP)
- SSL and TLS
- WireGuard
1. Remote Access VPN
If your boss wants you to travel but you still need to work while you are on a business trip, you just need remote access VPN to have a secure connection and encryption of your data. Remote Access VPNs are a vital tool for businesses that require employees to work remotely or travel frequently.
If an employee is not physically present in the office these VPNs provide a secure and encrypted connection that encrypts all the traffic or the signals sent or received by the user.
However, this type of VPN may not be the most practical solution for organizations that use software as a service (SaaS), as the data would be traveling from the user’s device to the central hub, to the data center, and back again, which could introduce bottlenecks and affect network performance. But still, this VPN can provide you with many benefits.
Benefits
- It enhances users’ way to access applications
- Maintains consistent security
- Apply security policies on any location
2. Site-to-site VPN
Many companies have multiple locations even overseas sometimes but they need to share a local area network to maintain work stability and network performance which can’t be possible by LAN, so that’s where Site-to-site VPNs come in handy.
They create a unified network that provides a permanent and secure connection between multiple offices. This type of VPN requires separate configurations for both networks and is great for businesses with multiple remote branches.
Site-to-site VPNs can be configured on-premises routers or firewalls. However, site-to-site VPN is not suitable for personal use or connecting from home, as administrators typically do not allow connections from networks they cannot control for safety reasons. Yet it has its benefits for businesses with multiple locations.
Benefits
- Site-to-site VPN provides a secure connection that encrypts every message on public interests
- It provides you with a simplified network architecture
- Access control, which let users on the other hand have access to their business data.
3. Internet Protocol Security (IPSec)
VPNs are based on protocols that let them give you a secure connection over the internet but that’s another story on how VPNs are based on protocols, but in this article, I am going to explain what are protocols and how they are better at their performance so starting with Internet Protocol Security (IPSec), which is a framework of open standards that provides robust security, confidentiality, integrity, and authenticity of data exchanged between two endpoints.
It enforces session authentication and data packets with twofold encryption, making it difficult for hackers to intercept. Amazing right? Before getting into a completely another we should get into the benefits of IPSec.
Benefits
- After implementation, IPSec provides you with strong security for all traffic crossing within the parameter.
- It is a transparent transport layer because of which there is no need to change any software or application when its implemented
- Can provide security to individual users too
4. Layer 2 Tunneling Protocol (L2TP)
IPSec provides security to smaller connections or businesses with one location whereas L2TP, or Layer 2 Tunneling Protocol, is a VPN tunneling protocol that establishes a connection between two points, L2TP uses an additional tunneling protocol, such as IPSec for providing an added layer of security.
Its complex architecture helps ensure the high security of the exchanged data, which makes it a popular choice for Site-to-site VPN setups where data security is necessary. Since it is a more secure and larger based protocol it has its benefits.
Benefits
- L2TP is considered to be the most secure and extremely fast since it has no vulnerabilities to slow it down.
- Compatible with every operating system
- It can be implemented in the simplest way possible.
5. Point-to-Point Tunneling Protocol (PPTP)
Point-to-Point Tunneling Protocol (PPTP) or old school protocol was established in the early 90s and was a successful protocol in its time but since there have been far more technologies in this era PPTP has its loopholes that can be broken down by hackers or different co operation, So PPTP creates a tunnel between two devices using a PPTP cipher.
However, the security of PPTP has been called into question due to the vulnerability of its encryption method. Computing power has increased significantly. As a result, the cipher can be easily brute-forced, making it an insecure choice for VPNs.
Benefits
- PPTP is compatible with every operating system.
- It has a user-friendly surface since it doesn’t need the encryption of data.
- It is a cheap setup compared to other protocols
6. SSL and TLS
After IPSec and L2TP, Secure Socket Layer (SSL) and Transport Layer Security (TLS) were invented and were completely based on cryptographic protocols that provide secure communication over the internet. They encrypt data exchanged between one end to another point to ensure confidentiality, integrity, and authenticity.
TLS is an updated and more secure version of SSL and is the standard protocol used for secure communication on the internet. Cryptography is completely based on blockchain and is considered to be the safest way to have communication on the internet while it has its own benefits.
Benefits
- Provides keyed messages and key hashing authentication
- Data travels from node to other node and provides a secure way of communication with no message alteration
- TLS provides with alert option about problems with a session and document
7. WireGuard
The world is running towards the higher end of technology, so, after SSL and TLS there is a new protocol WireGuard that helps you have a secure connection without any burden on your machine because of its lightweight design.
WireGuard is gaining popularity due to its simplicity and high-performance capabilities. WireGuard has faster connection speeds and lower latency because of its streamlining and efficiency. The state-of-the-art cryptography techniques make it a secure VPN connection.
Benefits
- WireGuard’s lightweight design doesn’t put a burden on your machine or network resources which makes it highly appreciated in the modern world
- It has a streamlined design that doesn’t use handshake authentication between users
- Using the latest cryptographic technology makes it extremely secure
In conclusion, VPNs are a great tool to protect your privacy, access restricted content, and enhance your online security. Whether you’re a frequent traveler or just want to ensure your online activities are kept private. As with any technology, it’s important to do your research By taking the time to learn more about VPNs and incorporating them into your online presence, you can enjoy a safer and more secure online experience.
FAQs about VPNs
What is a VPN?
VPN stands for Virtual Private Network. It is a technology that allows users to create a secure and private connection over a public network, such as the internet.
How does a VPN work?
A VPN works by establishing an encrypted tunnel between the user’s device and a remote server operated by the VPN provider. All the user’s internet traffic is routed through this tunnel, keeping it secure and protected from prying eyes.
What are the benefits of using a VPN?
Using a VPN offers several benefits, including enhanced online privacy and security, the ability to bypass censorship or geo-restrictions, anonymous browsing, protection from hackers and cybercriminals, and secure access to remote networks.
What are the types of VPN protocols?
There are several types of VPN protocols, including:
1. PPTP (Point-to-Point Tunneling Protocol)
2. L2TP/IPsec (Layer 2 Tunneling Protocol/Internet Protocol Security)
3. SSTP (Secure Socket Tunneling Protocol)
4. OpenVPN
5. IKEv2 (Internet Key Exchange version 2)
Which VPN protocol is the most secure?
OpenVPN is generally considered one of the most secure VPN protocols due to its strong encryption and open-source nature. However, the security of a VPN also depends on the implementation and configuration by the VPN provider.
Can I use a VPN on all devices?
Yes, VPNs can be used on a wide range of devices, including computers, smartphones, tablets, and even routers. Most VPN providers offer apps or software for various platforms and operating systems.
Are VPNs legal?
VPN usage is legal in most countries. However, it’s important to note that some countries have restrictions on VPN usage or may have specific regulations regarding their use. It’s advisable to check the legalities of using a VPN in your country or jurisdiction.
How do I choose a VPN service?
When choosing a VPN service, consider factors such as strong encryption, a no-logs policy, a wide network of servers, fast connection speeds, compatibility with your devices, good customer support, and positive user reviews.
Are free VPN services safe?
Free VPN services can vary in terms of safety and reliability. While some free VPNs may offer basic security, they often have limitations, such as data caps, slower speeds, or potential privacy concerns. It’s generally recommended to choose a reputable paid VPN service for better security and performance.
Can a VPN bypass censorship?
Yes, a VPN can help bypass censorship by encrypting your traffic and routing it through servers in unrestricted locations.
How does a VPN ensure privacy?
A VPN ensures privacy by encrypting the user’s internet traffic. This encryption scrambles the data, making it unreadable to anyone who intercepts it. Additionally, the VPN hides the user’s IP address, making it difficult to trace their online activities back to their real identity.

 18 biggest X (Twitter) Spaces in 2026
18 biggest X (Twitter) Spaces in 2026


![Top 10 Best FREE VPNs in [year] 2026 6 Best FREE VPNs that you can use today](https://noobspace.com/aglynyst/2023/05/best-free-vpns-120x86.jpg)
![11 Top Best Paid VPNs in [year] 2026 7 The top beset paid vpns of 2023](https://noobspace.com/aglynyst/2023/04/best-paid-vpns-120x86.jpg)
![How to watch Indian Premier League (IPL) [year] for free from anywhere 2026 8 Watch IPL live in 2023](https://noobspace.com/aglynyst/2023/04/how-to-watch-ipl-live-2023-120x86.jpg)
![11 Top Best Paid VPNs in [year] 2026 9 The top beset paid vpns of 2023](https://noobspace.com/aglynyst/2023/04/best-paid-vpns-75x75.jpg)
![Top 11 battery draining apps you should uninstall in [year] 2026 10 An illustration of low battery in a smartphone caused by apps](https://noobspace.com/aglynyst/2022/03/top-battery-draining-apps-75x75.jpg)